Why are we here?
Bottom line, because we know that Theodosiana can eliminate the threat and devastation of mass data breaches for your organization, and we believe that bringing this product to market is the most impactful thing we can be working on.
Let me explain:
It’s 2025, and as evidenced by the news headlines each week, it’s not hard to see that existing approaches to data security are not only flawed but are also too often failing us. We’re here to flip the script and change the way organizations protect and control access to their most valuable asset, their data.
Alongside my co-founder Andy, I have been building and selling software for over 20 years. Together, we've spent the past decade of our careers hyper-focused on delivering cybersecurity products and services to some of the most regulated and sensitive industries.
In that time, we've battled data breaches and insider threats for organizations ranging from Fortune 100 companies and multi-trillion dollar financial institutions to intelligence agencies. And as you might imagine, we learned a thing or two about how and why data breaches actually happen - how companies are actually being targeted, and why the existing cybersecurity toolset is failing.
Whether it’s a kid hacking from their basement or a sophisticated nation-state targeting classified data, the anatomy of a data breach is remarkably similar. The way attackers get in, the way they access and exfiltrate data, the failure of the security tools to identify the breach in a timely manner... It’s the same story over and over again.
But how is that possible? Why haven’t mega corporations investing billions into the cybersecurity sector, like Microsoft or Google, definitively solved this problem?
Over the years, we developed a thesis and a solution.
What Problem Are We Solving?
We’ll break this down further in the coming weeks and months here on our blog by sharing real-world examples, technical breakdowns, and customer stories/testimonials, but for the purpose of this introductory post, I will simplify it:
As has been the case for decades, the primary approach to protecting data (files, communications, databases, etc.) has been to put it behind a “secure” perimeter, and then to try and monitor/detect when that perimeter is breached.
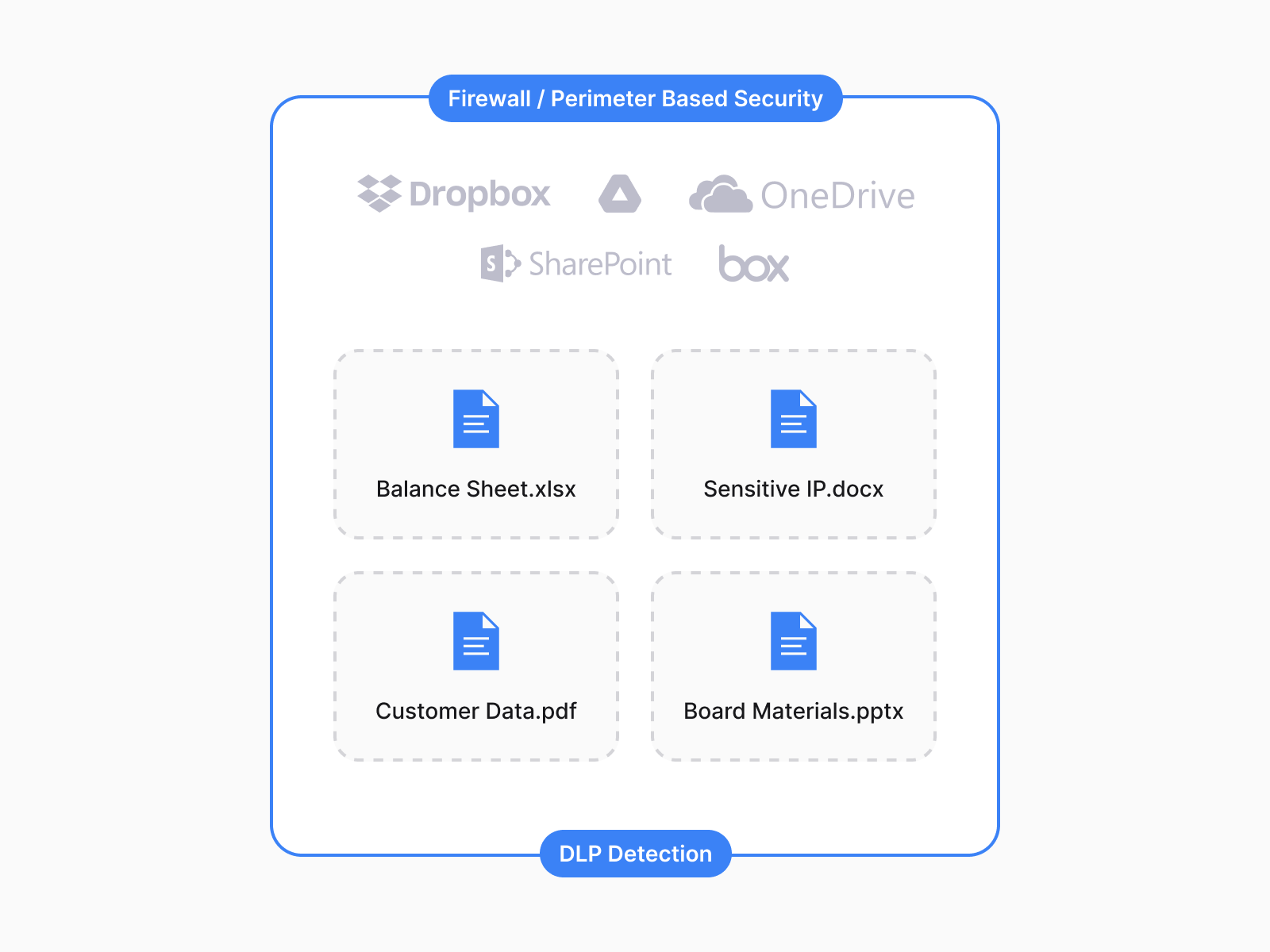
Whether it’s cloud software or your company’s corporate network, this is how most of the tools you use daily, like SharePoint, Google Drive, Dropbox, AWS, and even the computer or phone you are using now, work.
And yes, for our more technical audience, obviously it’s not quite that simple, and in the future we will dive deeper into the intricacies of in-transit and at-rest encryption, server-side vs. end-to-end encryption, etc., but for the general audience, let’s keep it high-level for now. In short, you take a file and put it in the cloud, or in your company’s Network Drive, alongside many other files, and access to the drive is controlled at the perimeter.
Again, as we can see from the parade of high-profile data breaches, there are many problems with this perimeter-based security approach.
One of the biggest challenges is that, in the real world, data doesn’t stay in one place. Even if you try to lock it down with technologies like DLP, employees and users move data. They email it around, they put it in apps and clouds that your company doesn’t control, they save it to their personal devices... Data moves, that’s reality, but your organization's "secure perimeter" doesn’t.
Because data moves, companies quickly lose control of their data - data leaks and insider threats galore. In particular, this is a huge problem for organizations operating in regulated spaces such as those handling CUI or ITAR data. They face enormous fines when their employees accidentally (or intentionally) move data out of the secure/compliant data store.
But an even bigger problem is that when all of your files are lumped together and protected by a single perimeter, attackers don’t need to probe for a server misconfiguration or try and break the firewall to get in, they can simply phish/spoof a single employee at your organization (which is crazy easy to do) and they suddenly gain the ability to bypass the perimeter entirely - to walk right through the front door.
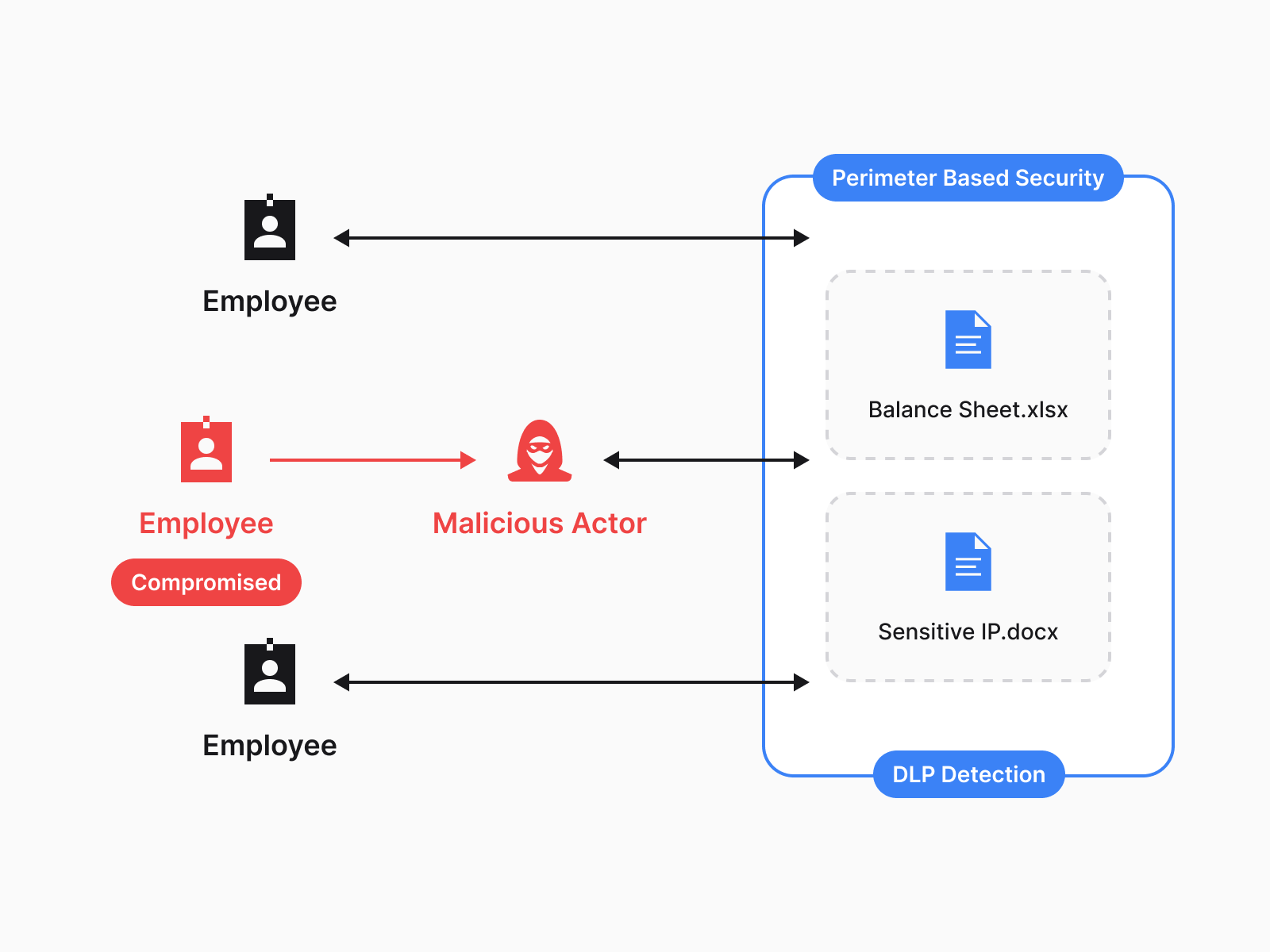
Once inside, the files within your company's SharePoint or Google Drive aren’t individually protected or controlled, resulting in what is called a mass data breach. This means that a breach of just one user, one server, or one device can equate to a breach of all of your company’s data. Yikes.
Worse still, the dirty secret of the cybersecurity industry is that even for Fortune 100 organizations, using the bleeding-edge anomalous activity detection and DLP tools to try to detect and/block unauthorized access or movement of data. It takes, on average, 200+ days for the organization to even detect that they've been breached. That’s not a typo; on average, attackers have 200+ days to sift around in your team’s Drive, network, etc. before anyone even knows they’re there!
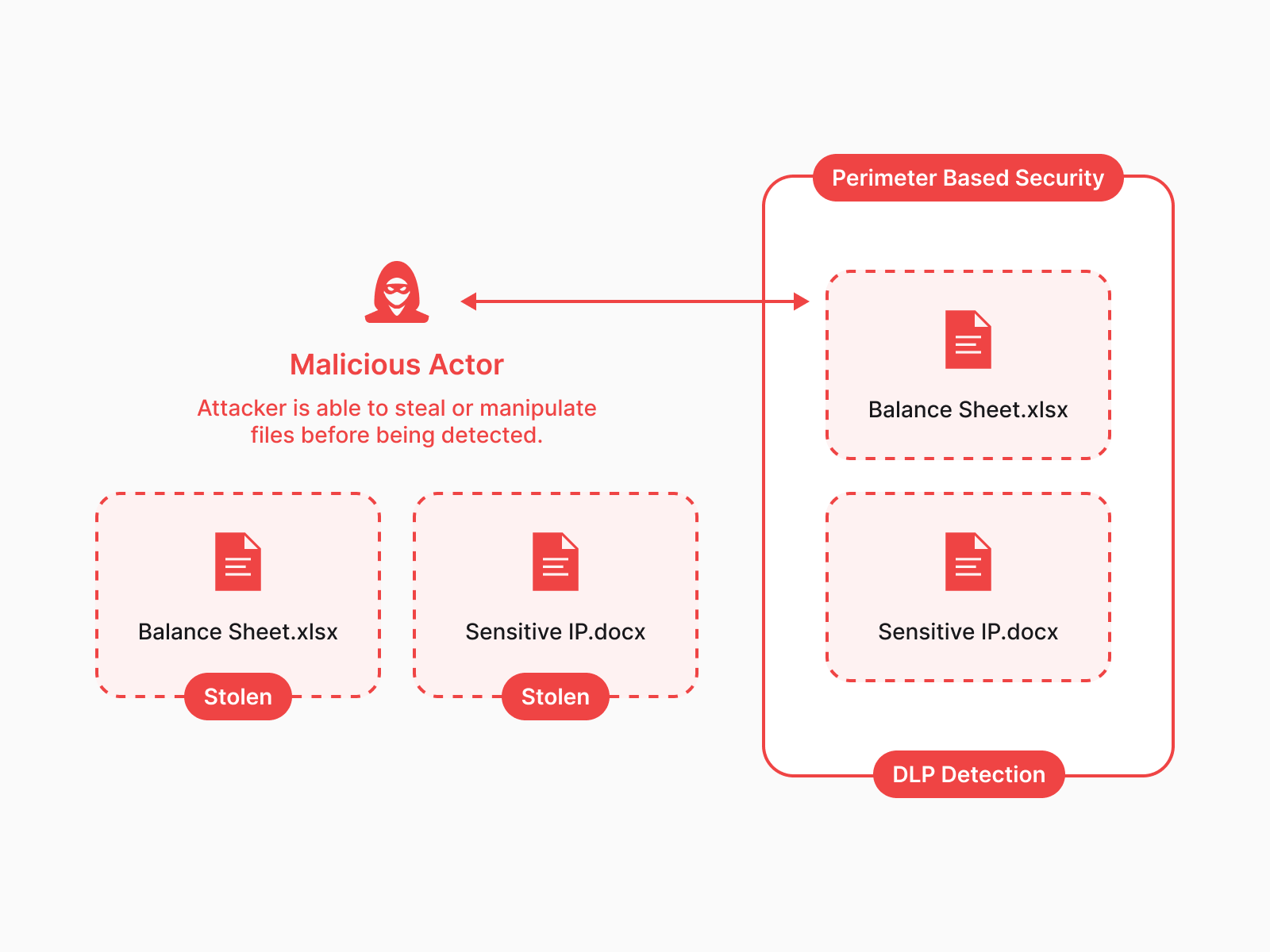
Needless to say, this reactive “detect the mass data breach 200 days after it has already happened” approach is not sufficient.
How is Theodosiana Different?
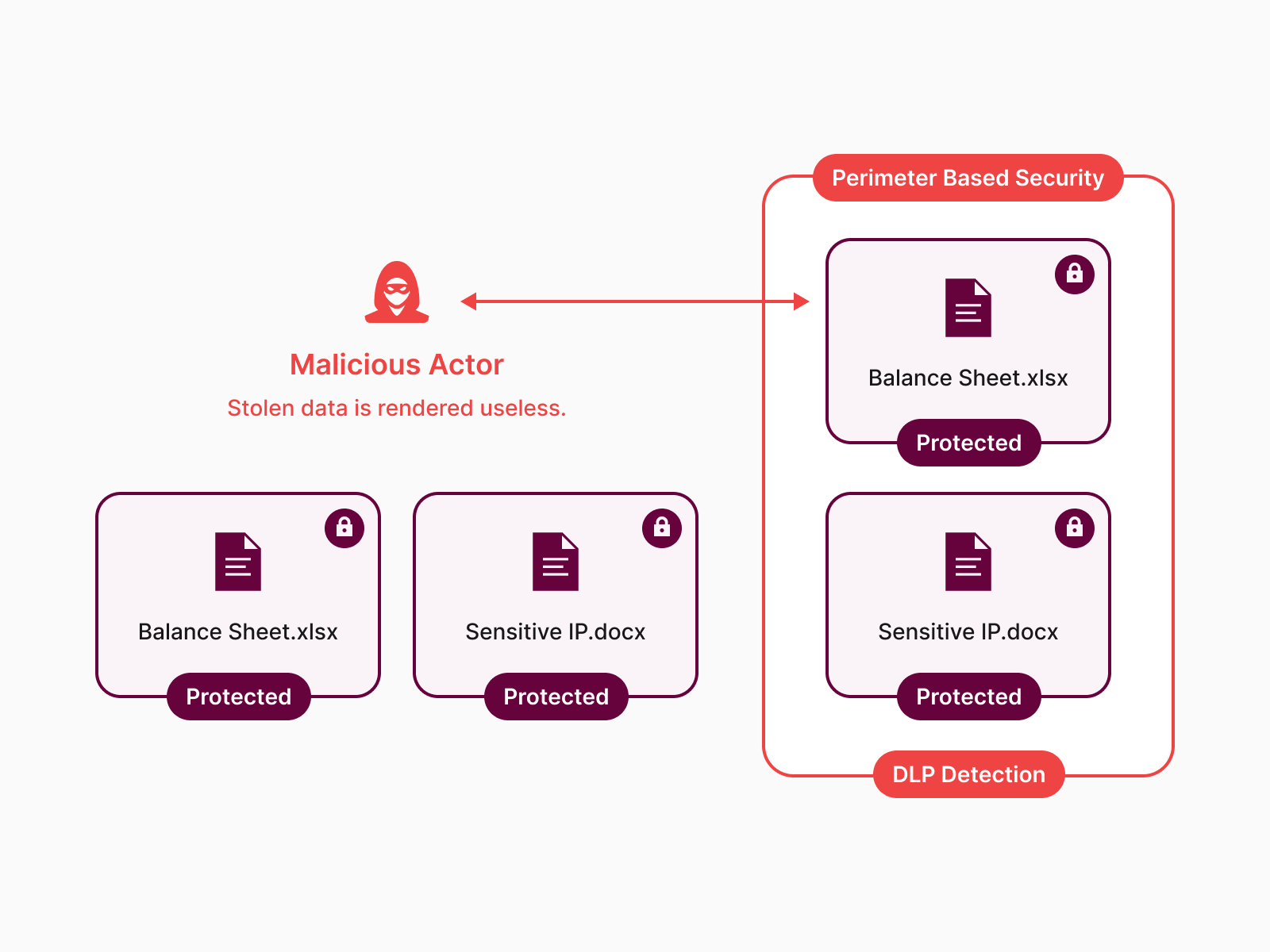
Theodosiana 100% flips the traditional data security model on its head. Instead of the security being applied at the perimeter, Theodosiana protects and controls access to each file individually.
With patent-pending technology, Theodosiana applies strong FIPS 140-3 validated, end-to-end encryption and per-file access controls that follow your data — wherever it’s created, stored, or transferred.
This means that when an organization suffers a breach or a malicious insider attempts to exfiltrate data, the bad actor walks away with individually protected files that they cannot access or decrypt!
And with rich audit logs and compliance dashboards, unauthorized/failed access attempts are recorded and anomalous activity is highlighted for your team to review, effectively reducing the "200+ days" it takes to detect a data breach.
What is Theodosian?
Theodosiana is a lightweight SaaS app that runs on all operating systems and plugs directly into your cloud or network drives in order to encrypt data where it is already stored and wherever new data is being created. The application is designed to be invisible to end users, running silently in the background without interrupting their day-to-day workflows.
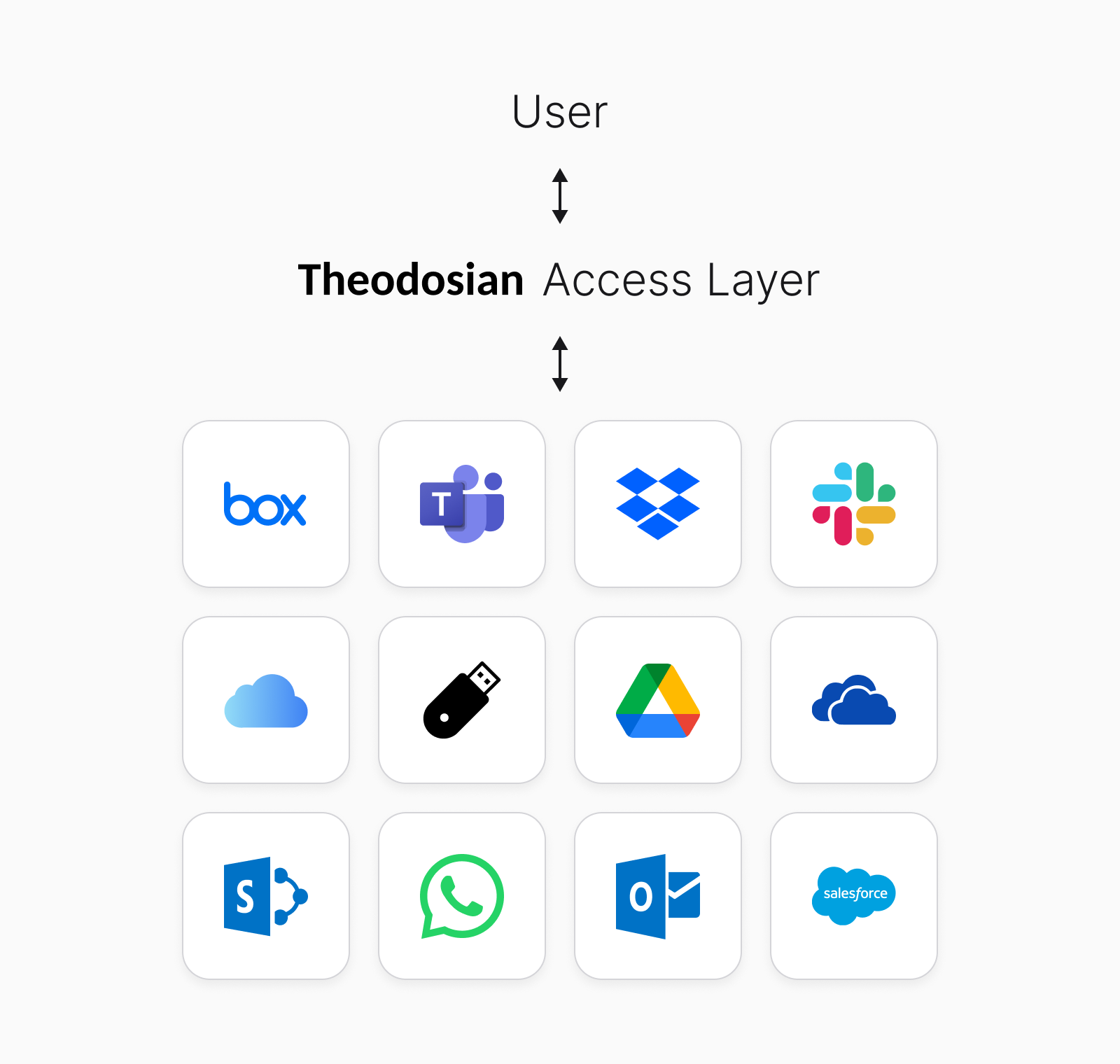
Going well beyond traditional DLP and perimeter-based security, Theodosiana encrypts and applies persistent access controls to files of any type or size, regardless of where the files are created or stored. The protection follows files wherever they are moved, whether that’s over email, Dropbox, USB sticks, etc.
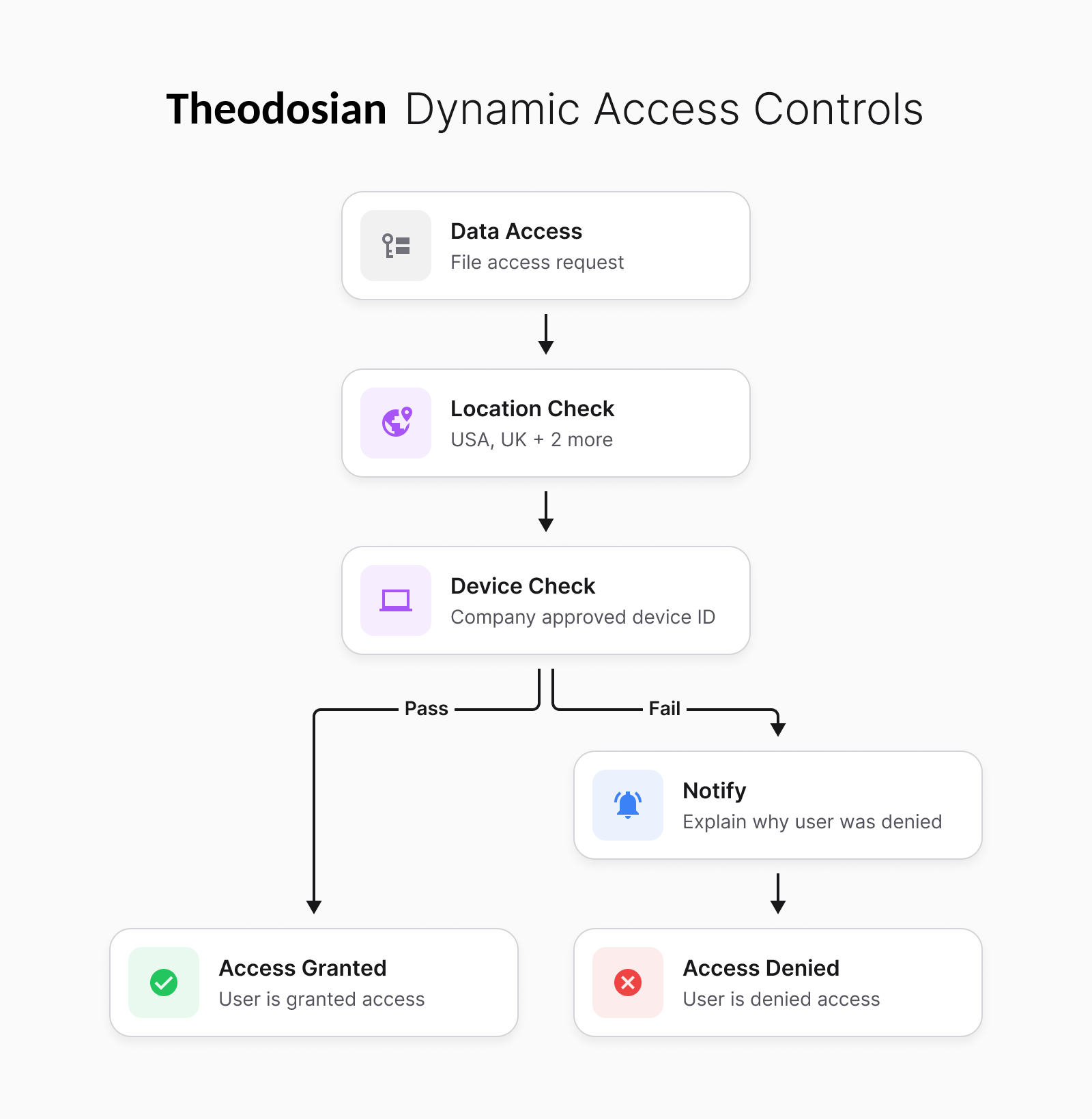
Theodosiana's dynamic and multi-layered access controls empower organizations with complete and persistent control over who, when, and where their protected data can be accessed.
Administrators can limit access to files based on user roles (RBAC) or even the attributes of a given file/user/device (ABAC). Different files and user groups can have different levels of authentication required to approve access, and many layers of authentication can be stacked on top of each other depending on the sensitivity of the data.
Why Now?
As we explained to our investors, there are two things converging at lightspeed that have made 2025 an ideal time to launch Theodosian.
The First is AI
In many ways, AI is an incredible tool and can be applied to aid in the cybersecurity stack, assisting with things like identifying bugs in code or identifying anomalous activity.
On the flip side, AI is also being employed by hackers, and it is enabling them to do things like spoofing, phishing, and vishing, on a scale once thought unimaginable. It’s quite terrifying.
Further, because widespread access to AI is relatively “new,” organizations and employees don’t understand the implications of doing things like uploading sensitive company files and IP to… ChatGPT (or any other model).
In short, it’s never been easier for employees to accidentally put company data at risk or commit compliance violations, and it’s never been easier for attackers to target your company with AI.
The second reason, while less exciting on the surface, is equally important.
Data Security Regulations & Compliance
Specifically, an all-new data security regulation called Cybersecurity Maturity Model Certification 2.0 (CMMC) was passed by the U.S. DoD and is coming into effect at the end of 2025.
Because of Theodosian’s unique security properties, it is an excellent tool to help organizations map to and achieve compliance with all kinds of data security frameworks (for example, HITRUST, GLBA, SOX, etc.), but maybe none are more complex or difficult to comply with than CMMC.
CMMC was developed by the DoD as a way to enforce strict data security standards on the defense supply chain and to protect sensitive data related to government contracts and projects. According to the Pentagon, there are currently more than 300,000 organizations in the US alone subject to CMMC compliance.
But it doesn't stop there - America's allies across NATO are following suit, with many countries, including the UK, launching their own versions of CMMC in the coming months and years, bringing data security to the forefront of national security.
Bonus: What Does “Theodosian” Mean?
The company is named “Theodosian” after the “Theodosiana Walls,” which were the fortifications built around the capital of the Eastern Roman Empire, Constantinople (modern-day Istanbul).

The Theodosiana Walls protected the Eastern Roman Empire from attackers for over 1,000 years (more commonly referred to as the Byzantine Empire, even though they referred to themselves as Roman, and “Byzantine” was a word historians invented hundreds of years later).
They were not only one of the most beautiful, but also one of the most effective fortifications of the ancient world.
Given the fact that here at this company, our sole mission is to defend our customers from attacks (cyber), we felt that naming the company after one of the most successful and important fortifications in history was extremely fitting.
Join us
Theodosiana solves an important data security problem. We’re passionate and excited about what we do, and we know that we can help you. So let’s talk!
We'd be happy to show you a demo, or at the very least, we can learn from each other. Together, let’s make mass data breaches a thing of the past.
Keen to See Theodosiana in Action?
See how protecting your files and simplifying compliance has never been easier.
